
Ever since the dawn of human civilization encryption has been a way to keep information from falling into the wrong hands. From Ceasar to the Enigma machine used in WW2; the strength of the crypto largely depends on the strength of the cipher used. In this article we will be looking at different protocols, encryption ciphers, overall security, reliability and speed.
PPTP
- PPTP: (Point-to-Point Tunneling Protocol)
One of the earliest and most widely used methods for VPN network implementation. PPTP’s specification was published in 1999 for VPN use on dial-up as a part of RFC 2637; formed by a vendor consortium that included Microsoft and others.
- Security of PPTP:
The PPTP specification does not outline any encryption or authentication features inherently built in. It relies on the PPP (Point-to-Point) protocol to implement security and various other authentication protocols such as: MS-CHAP-v1, MPPE MS-CHAP-v2 being the most common, EAP-TLS. MS-CHAP-v1 is so insecure that tools exist to extract the NT password hashes. MS-CHAP-v2 is vulnerable to dictionary attacks and can be cracked within as little as 23 hours. Bottom line is that all users and providers of PPTP VPN’s should migrate over to a different VPN protocol. Cracking MS-CHAP-v2 with a 100% sucess rate. In fact PPTP is so insecure that traffic flowing through it should be considered plain-tex,t or in other words unencrypted. Anyone including petty cyber criminals to three letter government organizations can snoop in on your connection and steal valuable information, possibly leading to monetary loss and identity theft.
L2TP/IPSEC
- L2TP & L2TP/IPsec: (Layer 2 Tunnel Protocol)
Created from a mix of two older tunneling protocols: Cisco’s L2F & PPTP back in 1999. L2TP was standardized in RFC 3193 and is now recommended as a replacement for PPTP where encryption is a must. The speed might be a problem due to the protocol’s use of UDP port 500; which is usually/easily blocked on corporate firewall systems. In addition, L2TP encapsulation causes it to be slightly slower than other protocols.
- IPsec:
Developed in 1992 at a Naval Research Lab, part of a DARPA (Defense Advanced Research Projects Agency) sponsored project. Then the NSA (National Security Agency) interfered and the open free versions of the protocols had been developed under NSA contracts. Not to mention that NIST (National Institute of Standards and Technology) also had a play in it. To this day there are a variety of very legitimate theories as to the NSA’s involvement in undermining the project and making the encryption purposefully weak.
* NSA employees participated throughout, and occupied leadership roles in the committee and among the editors of the documents * Every once in a while, someone not an NSA employee, but who had longstanding ties to NSA, would make a suggestion that reduced privacy or security, but which seemed to make sense when viewed by people who didn't know much about crypto. For example, using the same IV (initialization vector) throughout a session, rather than making a new one for each packet. Or, retaining a way to for this encryption protocol to specify that no encryption is to be applied. * The resulting standard was incredibly complicated -- so complex that every real cryptographer who tried to analyze it threw up their hands and said, "We can't even begin to evaluate its security unless you simplify it radically". See for example: https://www.schneier.com/paper-ipsec.html That simplification never happened.
- Security of L2TP and L2TP/IPSec:
By itself L2TP is just a tunneling protocol, it doesn’t provide any kind of encryption making it insecure. However paired with IPsec it makes for great “coffee shop Wi-Fi” encryption and will undeniably protect your data from almost anyone except the government. If you want to protect your privacy from the prying eyes of the NSA, then it’s suggested to turn a blind eye to this protocol entirely.
SSTP
- SSTP: (Secure Socket Tunneling Protocol)
Introduced by Microsoft in Windows Vista SP1 and Longhorn server in 2007. Developed with hope to reduce help desk support issues linked to IPSec VPN connections being filtered (blocked) by routers or corporate firewalls. SSTP uses SSLv3 thereby running on TCP port 443 (the same port HTTPS/SSL/OpenVPN use), this causes the traffic to be indescribable from regular encrypted HTTPS (Hypertext Transfer Protocol over Secure Socket Layer) webpages. Another advantage as stated above is that port 443 is hardly ever blocked by routers/firewalls due to its necessity of being open so that regular (HTTPS) web pages may load without issues.
- Security of SSTP:
SSTP configured correctly using a strong AES cipher can be very secure. Nonetheless, taking into consideration that SSTP was developed by Microsoft and is proprietary (code is not open to the public eye and could have a possible backdoor in it).
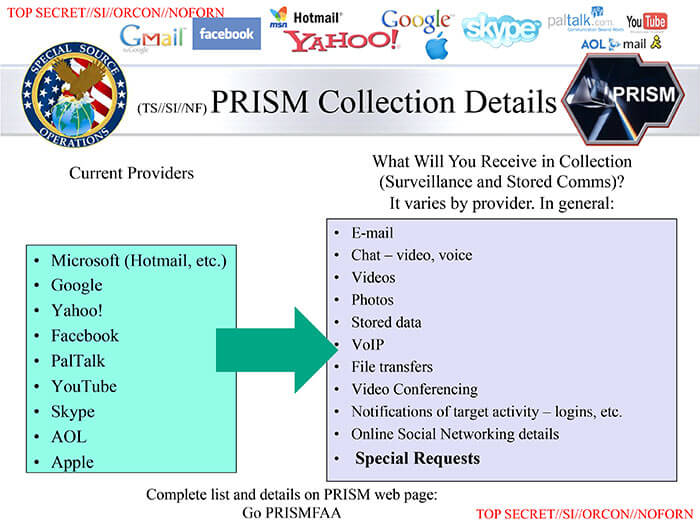
In addition, when we look back at Microsoft’s shady history of NSA co-operation during the PRISM surveillance program. The bottom line is that the SSTP protocol is good against cyber criminals at best but will not keep your data secure from G-men.
OpenVPN
- OpenVPN: Open source VPN software that was released in 2002 under the GPL License. It is capable of easily getting around firewalls and routers due to it running on TCP port 443, thus making it easier for the end user to connect to his or her VPN. OpenVPN is supported across a multitude of operating systems including Windows, Linux, Tomato/DD-WRT Routers, iOS, Android, and Mac OS X. Speed is another great quality of this VPN protocol, when configured properly in most cases it can easily outperform L2TP/IPSec. It is highly configurable and supports an incredible range of encryption algorithms.
- Security of OpenVPN:
This is by far the most secure VPN protocol; even NSA whistle-blower Edward Snowden himself confirmed that OpenVPN has not been backdoored nor compromised by the NSA. The fact that OpenVPN uses the OpenSSL library means it can provide the end user with a variety of hardened ciphers.
The major ones include:
- AES (Advanced Encryption Standard, in use by the U.S. government)
- Blowfish
- Camelia (Comparable to AES, but NIST had no part in development making it arguably securer from the NSA)
- SEED (Block cipher developed by the Korea Information Security Agency)
- CAST-128 (Approved by the Canadian government and in use by CSEC – Communications Security Establishment Canada)
- Triple DES (Built upon the Data Encryption Standard with increased key size to protect against attack vectors that worked against the original DES)
- GOST 28147-89 (Designed by the KGB [Soviet Union’s Committee for State Security] declassified and released to the public in 1994, it was the Soviet alternative to the U.S. DES algorithm)
Not to mention perfect forward secrecy or PFS, which means that a session key derived from long-term keys cannot be compromised if the long-term keys are compromised. (e.g. Makes it so that encryption keys are ephemeral [lasting for a very short period of time]) In simple terms, guards against the NSA capturing a key from one conversation between you and your VPN and having subsequent conversations with you/your VPN server using that same captured key!
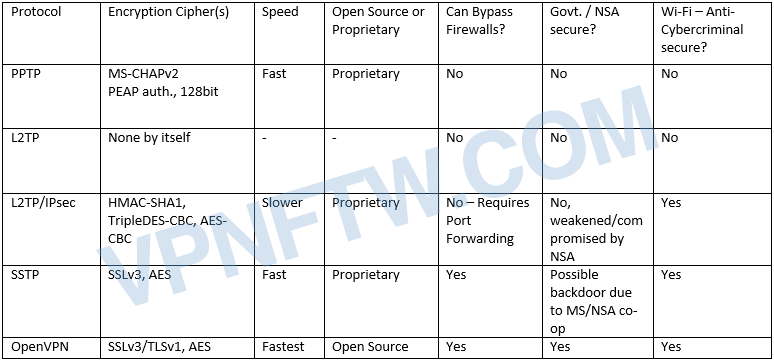
Below is a small picture to sum up the protocols with their security, speed, and firewall bypass limits.
While it is sad we have to make a list of the best encrypted VPNs on the market, it needs to be done. Too many providers are offering gimmicky firewalls and low-level encryption.
Best Encrypted VPN Providers
LiquidVPN
LiquidVPN – LiquidVPN is one of the most secure VPN’s due to the encryption it uses. As noted above, many encryption protocols are approved by the National Institute of Standards and Technology (NIST). NIST is directly correlated with the government, meaning if the algorithm is approved, it should be noted as backdoored. LiquidVPN decided to take a step in the right direction and use non-NIST protocols. LiquidVPN offers 4096 DH and RSA keys, 20 minute perfect forward secrecy key re-negotiations, and TLS-Auth HMAC firewall. This is their standard protocol right from the CEO, Dave Cox. While LiquidVPN offers top of the line encryption and is certified with perfect forward secrecy, they also offer a secure DNS, intrustion prevention system, and an IP modulation system. The infrastructure in itself is extremely secure in the way it operates.
Pros:
- Uses secure non-NIST algorthms
- Non-logging provider
- Offers non-logging, secure encrypted DNS
- Offers IP modulation
- Offers intrusion prevention system
- Offers setup for almost any device
- Perfect forward secrecy
Cons:
- Operates under the jurisdiction of the United States of America
Visit the LiquidVPN Website here and get %20 off!
CryptoStorm
CryptoStorm – CryptoStorm is the rebirth of its previous company, CryptoCloud. Getting right to encrypted, CryptoStorm knows exactly what they are doing. In their CryptoStorm Interview, the company states they use auth SHA512, cipher AES-256-CBC, replay-window 128 30, tls-cipher TLS-ECDHE-RSA-WITH-AES-256-SHA, and to top if off they utilize perfect forward secrecy. Not only does CryptoStorm has a bomb shelter infrastructure, they top it off with anonymity. CryptoStorm is the first provider to ever utilize a token based authentication method. This means whatever payment the user pays with, it will be anonymous. There are no username, passwords, emails, or any data. The user recieves a token and connects with that. CryptoStorm holds no customer data, and has thousands of active tokens being used at once. The privacy they offer is new age, and they operate a secure infrastructure.
Pros:
- Offers secure infastructre
- Perfect forward secrecy
- Offers setup across almost any device
Cons:
- Don’t state to use non-NIST algorithms
- Guides aren’t extremely detailed, could use work
Visit the CryptoStorm Website!
VPNSecure
VPNSecure – VPNSecure is a bit of a newer service that too offers a secure infrastructure. In their interview the company notes they use 2048 bit Keys, available both UDP and TCP. VPNSecure offers some additional features with add-on proxies and a smartdns. Overall the service appears secure from the outside.
Pros:
- Offers secure 2048 bit keys on OpenVPN
- 33 countries to connect to
- Offers computer clients and OpenVPN on mobile devices
Cons:
- A bit newer and smaller company
Visit the VPNSecure Website!
Overall
Encryption is one of the backends of security in a VPN. Poor encryption implementation means the traffic can be easily decrypted and read. Strong encryption will fend off malicious attackers, government agencies, the NSA, and just about anyone trying to snoop on traffic. Even lower-level attackers can decrypt poorly implemented encryption algorithms with ease. Always be sure to choose a VPN wil strong encryption, or the service is essentially useless.
Picture Credit: Icon made by Freepik from www.flaticon.com


